
The trouble about Apple (in)Secure Enclave
Finally they did it!
Chinese team Pangu found a security flaw that allows access to content stored on Apple Secure Enclave, the coprocessor charged to store credentials, credit card numbers and other sensible informations on your iDevice.
More details can be found on this article of MacWorld and affects all devices starting iPhone 5s to iPhone X, iPads of 5th, 6th and 7th generation and iPad mini 2, 3 and 4.
So, plenty of devices!
The great news is that to violate your device’s security enclave, crooks has to physically access your iDevice: An attack cannot be performed remotely; once again please be very careful about how to use your device!
The bad news is that this flaw cannot be repareid: It’s an hardware problem.
New devices are not affected by such issue.
I’d like to spend some words about AnoniCloud.
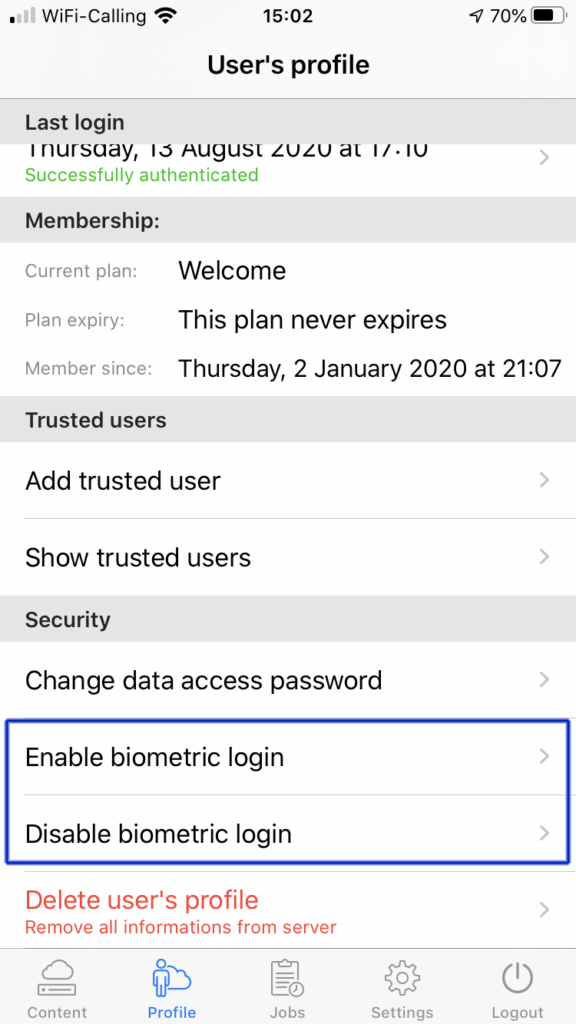
Since the beginning, here at AnoniCloud, we believed that the safest place to store your credentials is your brain. In the early beta we voluntarily avoided to support storing credentials in your keyring (so into secure enclave) but user’s feedback was clear: Provide biometric access, provide automatic login when app open, so store credentials on device.
We satisfied user’s requests providing the best of both worlds: Our users can explicitly choose to store their credentials on keyring to allows such login comforts or disable everything (it’s our default!) and manually insert username and password.
Just be warned and aware that your device is a very complex machine, built above billions of transistors (hardware) and lines of code (software) that is the result of the job of several engineers spread around the world: The matter is not if it’s contains bugs but how many bugs it contains.